That’s the technical term for this.
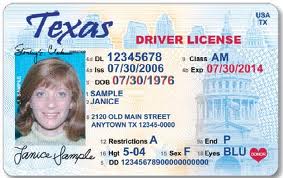
The Texas Department of Public Safety was duped into shipping at least 3,000 Texas driver’s licenses to a Chinese organized crime group that targeted Asian Texans, DPS Director Steve McCraw told a Texas House committee on Monday.
The crime group worked through the state’s government portal, Texas.gov. The agency, which discovered the security breach in December, will begin notifying victims in letters to be sent out this week, the DPS chief said. More victims are still being identified, he said.
“We’re not happy at all, I can tell you that, one bit,” McCraw said in testimony to a House Appropriations subcommittee. “They should have had — controls should have been in place, and they never should have happened.”
The crime organization, which McCraw did not name, was able to get its hands on the Texas driver’s licenses by first pulling personal data on individuals with Asian surnames from the “dark web” and other underground data-trading portals.
That info, including previous addresses and family names, allowed thieves to correctly answer password security questions on the Texas.gov site and use stolen credit cards to order duplicate copies of active licenses — such as those ordered by people who misplace their licenses or report them stolen. A replacement license costs $11.
The state-run Texas.gov site is the central portal for Texans wanting to renew licenses, obtain driving records and registration, and obtain birth and death certificates, among other things.
The investigation into the stolen driver’s licenses spans at least four states and also involves fraudulent licenses duplicated from victims in other states as well as Texas. The FBI and the Department of Homeland Security are also investigating, according to the DPS letter to lawmakers.
House Appropriations Vice Chair Mary González, an El Paso Democrat, blasted DPS agency chiefs for letting so much time lapse while Texans were unaware that their identities were being used fraudulently.
“Somebody could be going around as Mary González right now for two months, and nobody’s been notified, I [wouldn’t have been] notified,” González said.
DPS officials are not calling the incident a “data breach” because they say no hacking was involved and vast amounts of data were not being stolen. Instead, the crime group used data obtained from underground sources to bypass a simple password security system — laying bare a security vulnerability that “should never have happened,” McCraw said.
Texas.gov is operated not by DPS, but by the Texas Department of Information Resources.
DPS officials declined to provide details about the security loophole that left the site open to fraud but told lawmakers that it had been closed.
DIR spokesperson Brittney Booth Paylor dismissed the notion that the incident was a cybersecurity breach, calling it “a case of fraudulent criminal activity based on factors unrelated to state systems.”
[…]
The problem was first detected in December when a third-party Texas.gov payment vendor “alerted DPS to an increase in customers challenging credit card charges for online transactions,” according to a February letter sent to lawmakers from the DPS. The credit cards used to buy the fraudulent copies were also stolen, authorities said.
Before investigators shut down the operation, McCraw said, the license thieves were able to use the site, billed as “the official website of the State of Texas,” to obtain driver’s licenses that are “Real ID compliant” — not cheap copies, McCraw said.
These stolen licenses can pass verification methods and be used fraudulently all over the country because they are real driver’s licenses being used by people who can pass for the photo on the original card, McCraw said.
See here if you want to learn a bit more about what a credential stuffing attack is. Long story short, don’t reuse your passwords and enable two-factor authentication where you can.
Putting my cybersecurity hat on for a minute, I will say that the DIR response to this is disingenuous. It’s true that there are plenty of pwned password lists available on the internet, and that it’s not Texas’ fault if people reuse passwords. But there are services that the state can subscribe to that would alert them to email addresses in their database that have been found in those pwned lists, which would then give DPS or DIR or whoever would have that responsibility the impetus to contact those address owners proactively and tell them to update their password. They could also enforce, or at least offer, a two-factor solution, and there are other proactive steps available as well. DPS/DIR isn’t “responsible” for this, but DPS/DIR absolutely could have done something to prevent or minimize it.
Rep. González’s complaint about the delay in notifying the affected users is addressed in a later Chron story. I drafted this originally Monday night, so I will do a separate post on that. Short answer, there is a legal requirement in Texas to report data breaches, but there is an exception for when there is an active law enforcement investigation, which DPS has invoked here.
Given the upsurge in violence against Asian-Americans, Rep. González also asked if this could be considered a hate crime, which McCraw avoided answering. It may not be possible to tell from what they know right now, but it is possible to try to figure it out. I’m glad DPS is in contact with the FBI and DHS about that, and I hope that leads to some action. I hope the Lege will press DPS and DIR to do better, and to share the results of the investigation when it’s over. The Lege – and the media – should also focus on McCraw’s statement about controls not being in place and demanding to know what is now being done about that. Either we learn from this or we risk having it happen again. The Chron has more.

Pingback: So about that DPS delay in notifying the victims of the credential stuffing attack – Off the Kuff
Pingback: Texas blog roundup for the week of March 6 – Off the Kuff